Single sign-on (SSO) is a property of access control of multiple related, but independent software systems. With this property, a user logs in once and gains access to all systems without being prompted to log in again at each of them.
The Central Authentication Service (CAS) is a single sign-on protocol for the web. Its purpose is to permit a user to access multiple applications while providing their credentials (such as userid and password) only once. It also allows web applications to authenticate users without gaining access to a user's security credentials, such as a password. The name CAS also refers to a software package that implements this protocol.
In this blog, you can find steps for setting up CAS server and integration with Liferay.
Outline :
Setup Information :
OS: Ubuntu 14.04
JDK: 1.7
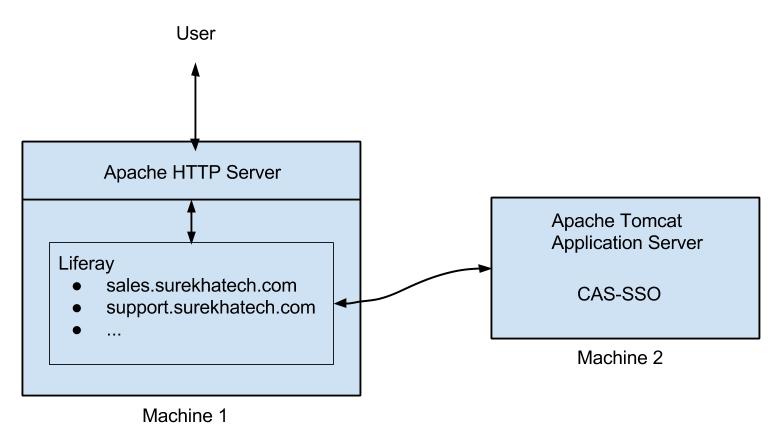
Machine 1: Apache HTTP Server, Liferay (6.2 CE GA 3) with multiple sites
Machine 2: Apache Tomcat 7 for CAS (JASIG CAS 3.5.2)
Setup CAS server
We will use sso.surekhatech.com as host name to access the CAS app.
We will generate a certificate and a key for the host “sso.surekhatech.com” with OpenSSL command line tool.
sudo openssl req -x509 -nodes -days 7300 -newkey rsa:2048 -keyout sso-surekhatech.key -out sso-surekhatech.crt
Followings are the details to fill up to generate the files:
Country Name (2 letter code) [AU]:IN
State or Province Name (full name) [Some-State]:GJ
Locality Name (eg, city) []:AHM
Organization Name (eg, company) [Internet Widgits Pty Ltd]:ST
Organizational Unit Name (eg, section) []:DEV
Common Name (e.g. server FQDN or YOUR name) []:sso.surekhatech.com
Email Address []:[email protected]
This will generate following two files:
- sso-surekhatech.key
- sso-surekhatech.crt
openssl pkcs12 -export -out sso-surekhatech.pfx -inkey sso-surekhatech.key -in sso-surekhatech.crt
open up $TOMCAT_HOME/conf/server.xml and locate the block that looks like this:
Add following tag :
<Connector port="8443" protocol="HTTP/1.1" SSLEnabled="true"
maxThreads="150" scheme="https" secure="true"
clientAuth="false" sslProtocol="TLS"
keystoreFile="/home/st24/Projects/CAS/keys/sso-surekhatech.pfx"
keystorePass="test" keystoreType="PKCS12" /> Note : keystorePass="test" ? Password @ time of pfx file creation
Then save the file. If you have Tomcat started, you'll need to restart it to enable the additional connector. You should then be able to access Tomcat over: https://sso.surekhatech.com:8443
(Tip : add host entry for sso.surekhatech.com to access the server.)
-
Download: cas-server-3.5.2.zip
-
Get cas-server-webapp-3.5.2.war from extracted zip file from following directory /cas-server-3.5.2/modules/
-
Deploy cas-server-webapp-3.5.2.war into tomcat’s webapp folder. After successful deployment, hit following into the browser https://sso.surekhatech.com:8443/cas-server-webapp/login
You can see the cas login screen. give following credential to test the login.
id: test
password: test
(Tip : The default configuration of the cas uses SimpleTestUsernamePasswordAuthenticationHandler, which authenticates the when user provides id=password. We can change the authentication handler as per our need.)
Liferay CAS/SSO Integration
You can download this certificate file by hitting https://sso.surekhatech.com:8443 in your browser. (Tip : add a host file entry with Machine 2 ip address, before you try to hit SSO server)
Following is the command to import certificate file into JVM keytool.
sudo keytool -import -keystore /usr/lib/jvm/java-7-oracle/jre/lib/security/cacerts -alias sso-surekhatech -file /{path-to-certificate}
Create a sites in liferay with following virtual host : sales.surekhatech.com
(Tip : goto LR control panel ? site ? Site-setting ? Site URL ? Virtual Host and set following virtual hosts for respective sites.)
cas.auth.enabled=true
cas.import.from.ldap=false
cas.login.url=https://CAS_SERVER_HOST_NAME:8443/cas/login
cas.logout.url=https://CAS_SERVER_HOST_NAME:8443/cas/logout
cas.server.name=LIFERAY_HOST_NAME:8080
cas.server.url=https://CAS_SERVER_HOST_NAME:8443/cas
cas.no.such.user.redirect.url=http://LIFERAY_HOST_NAME:8080/web/guest/nouserfound
cas.logout.on.session.expiration=false
For more implementation details or support you may contact us at [email protected].
For professional paid support, you may contact us at [email protected] .